Instill confidence in your connected products
Automated product security for connected devices and embedded systems, including: IoT, OT/ICS, Medical Devices, Connected Vehicles, and more.
Firmware isn't safe unless it's safe by design.
With over 20 billion internet connected devices today, connectivity is changing the world. For manufacturers, the ability to create new IoT, OT, and other connected devices and embedded systems has far outpaced their ability to keep those devices secure. Finite State is here to change that.
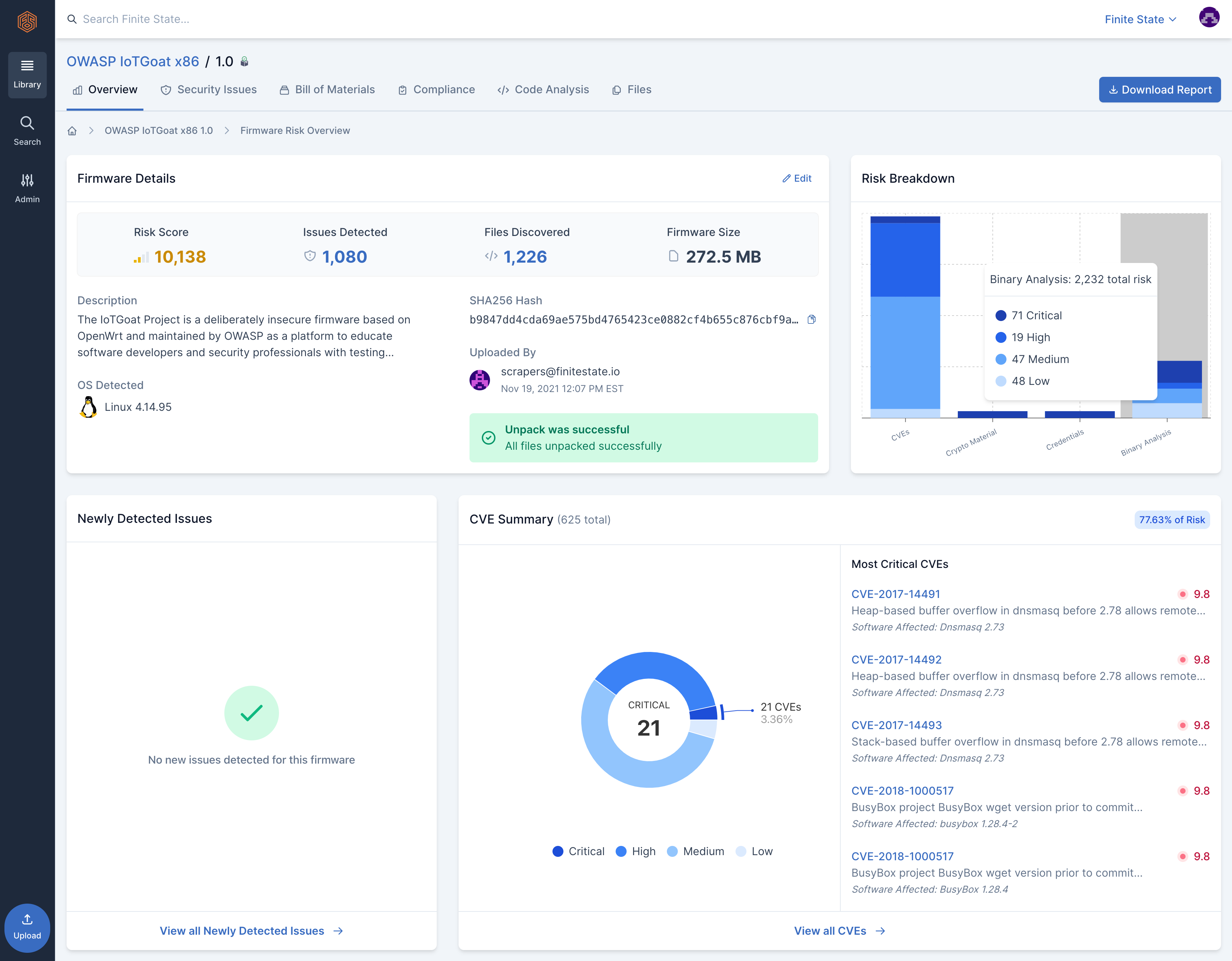
See everything
You can’t protect what you can’t see. Identify all device components, including third-party and open source.
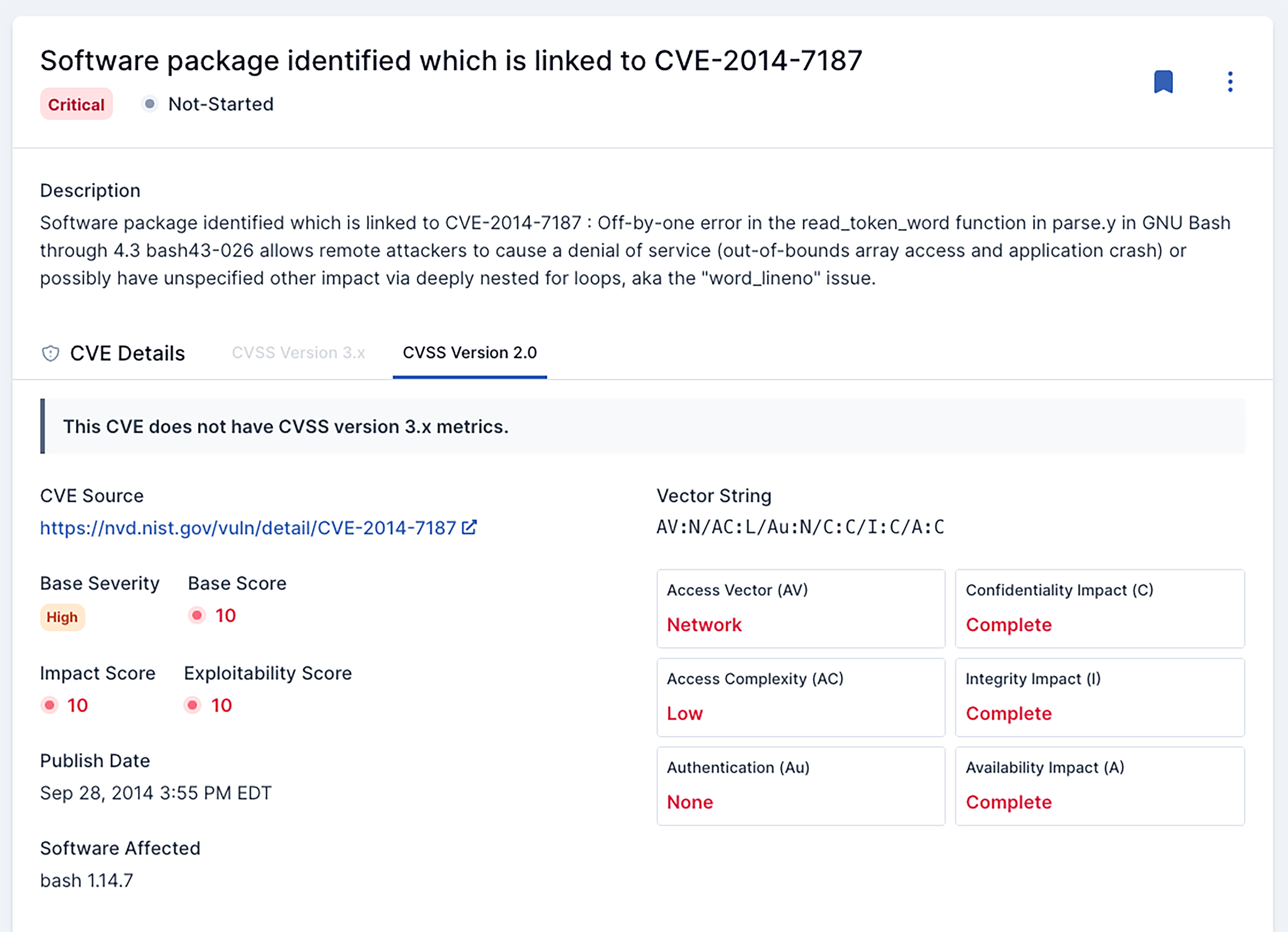
Secure everything
From hard CVEs to insecure configurations, the Finite State platform automatically uncovers security issues throughout your product portfolio and supply chains.
Get a free SBOM
Simply send us your firmware and we'll handle the rest.
“Finite State provides a holistic approach to analyzing devices, and the supply chain that underpins them.... We are excited to form this partnership to further support our customers with shifting security left into the design and development of these innovative products.”
Peter Ellis
VP Corporate Development, Veracode
A Full Context Approach
Our automated platform provides the most comprehensive solution for device manufacturers who want to secure their connected products. Here are some of the key features and benefits you can expect as a Finite State user:
Visibility
- Illuminate risk in first- and third-party code through Device Composition Analysis (DCA)
- Produce a comprehensive, machine readable Software Bill of Materials (SBOM) for every firmware version and every device
- Gain a comprehensive view of device components including drivers, boot loaders, configuration files, etc
- Quickly see which of your products is affected when new vulnerabilities are reported for faster remediation
Simplicity
- Test and analyze at scale with automated firmware analysis capabilities
- Seamlessly integrate into existing Agile / DevOps workflows
- Available via on-prem or in the cloud
- No source code needed: Simply upload final firmware images
- Receive quick and accurate results, including actionable security metric
Protection
- Enhance product cyber resilience by testing at every stage of the development lifecycle
- Quickly prioritize security issues in order to address those most critical to your product and business
- Manage supply chain risk by gaining deep visibility into third party and open source components and their security issues
- Resolve security issues early and often with remediation guidance
- Protect devices while maintaining production and development schedules
Confidence
- Meet evolving federal and industry standards and regulations with ease
- Convey key information to internal and external stakeholders with robust reporting capabilities
- Shorten time-to-market by providing proof of security and testing to customers and regulators

