Automated Compliance. Continuous Proof.
From development through post-market, the Finite State Platform automates SBOMs, vulnerability checks, and evidence reporting—so every device meets requirements at every stage. With always-on compliance, you can eliminate last-minute audit scrambles and certify by design from day one.
When Design Intent Drifts, Risk Creeps In
Threat modeling and security requirements are often:
- Created as one-time exercises that go stale
- Maintained in disconnected documents and tools
- Difficult to update as architecture changes
- Detached from what ultimately ships
The result is growing gaps between design assumptions and the software teams ultimately ship.
Finite State makes design-time security a maintainable, continuous workflow that stays connected to shipped software.
Architecture, threats, risks, requirements, and verification evolve together from design, to build, to release.
Instead of static threat models, teams work from living design intent that can be reviewed, verified, and defended across releases.
One-Click Compliance, Built Into Your Workflow
From development to deployment, compliance is automated at every step. Your ready-to-share audit evidence pack –SBOM, VEX, policy logs, and remediation status – is always just one click away
Generate SBOMs (Every Build)
Automatically produce SBOMs from source and binaries for every build.
Unify & Enrich SBOM Data
Combine build and supplier SBOMs into a single, enriched view of components and risk.
Enforce Policies in CI/CD
Check each build against compliance policies and block non‑compliant components before release.
Automate Documentation & Certification
Generate regulator-mapped evidence packs (SBOM, VEX, policy logs) on demand for EU CRA, CE RED, FDA §524B, and Cyber Trust Mark submissions.
Continuous Compliance Monitoring
Keep your SBOM and VEX current as vulnerabilities and standards evolve; receive targeted alerts based on product exposure.
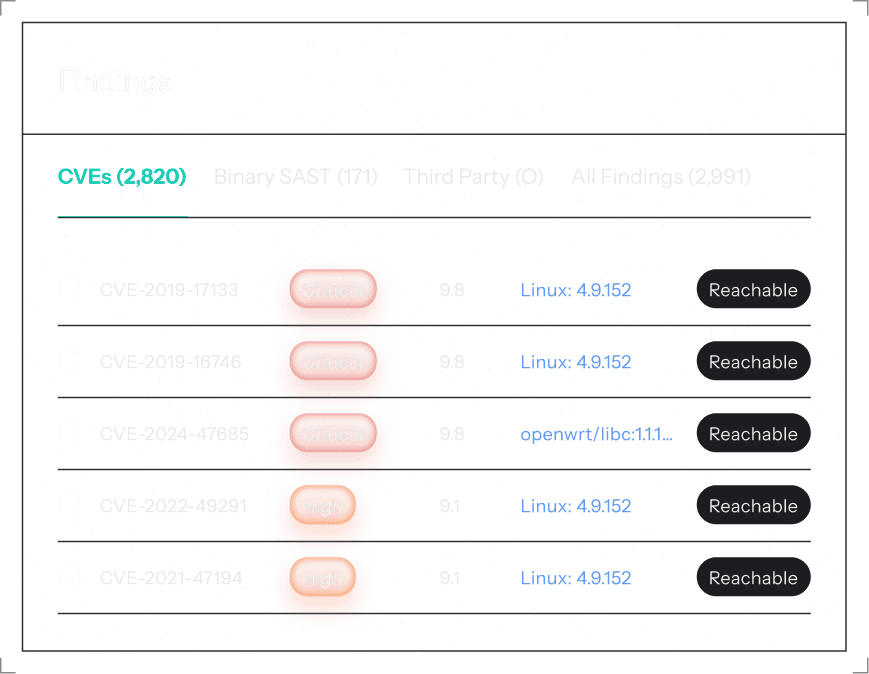
Uncover Hidden Vulnerabilities
Deep Binary Analysis
Our patented binary analysis engine finds vulnerabilities that traditional scanners miss. Deep firmware inspection reveals the complete attack surface in connected devices.
Binary reverse engineering for 130+ formats
Firmware component extraction and analysis
Cryptographic library vulnerability detection
Embedded system-specific CVE discovery
Supply chain component tracing
Unified Risk View
Source + Firmware Intelligence
Correlate findings across source code, firmware, and third-party components. Unified risk scoring eliminates blind spots and provides complete visibility.
Source code + binary correlation
Third-party component risk mapping
Exploit intelligence integration
CVSS scoring with context
Real-time threat feed correlation
Fast-Track Remediation
One-Click Fixes
Integrate security fixes directly into your development workflow with PR-ready diffs, automated PRs, and policy enforcement.
PR-ready diffs for supported components
Pull request automation
CI/CD policy gates
Developer workflow integration
Rollback-safe deployments
Continuous Monitoring
Post-Deployment Protection
Never miss a new vulnerability. Continuous monitoring watches for emerging threats and automatically assesses their impact on your deployed systems.
Real-time CVE monitoring
Automated impact assessment
Threat intelligence feeds
Post-market surveillance
Regulatory compliance alerts
Evidence packs for EU CRA, FDA §524B, CE RED
Autonomous Assurance
Reachability, KEV, and EPSS
Suppress noise with reachability analysis, KEV/EPSS signals, and policy context. Natural-language triage when you need it.
Reachability-based prioritization
KEV/EPSS exploit intelligence
Automated triage decisions
Natural language queries
Focus on the critical few
Take the Bottlenecks Out of In-House Pen Testing
Automate discovery, enrichment, and exploitability analysis to give pen testers actionable starting points and continuous context. Purpose-built for embedded and IoT, Finite State cuts weeks of manual effort from every test.
Zero Blind Spots
Unify source + binary visibility; unpack firmware to find what source-only or web-app tools miss.
Fix the 1%
Reachability + threat intel prioritize what’s truly exploitable; skip the CVE noise.
Built for Embedded
Works across 130+ formats / 30+ architectures / 18+ languages; purpose-built for devices & firmware.
Compliance, On Demand
Export evidence packs aligned to CRA, FDA §524B, ISO 21434—right from the platform.
Bring Your Evidence, No Matter Where It Starts
Centralize everything you need for defensible product security and compliance outcomes.
Vulnerability feeds and compliance data for enrichment
Container images, archives, and firmware packages
Binary and source code uploads from build pipelines
Third-party SBOMs from suppliers and partners
If it ships with your product—or arrives from your supply chain—we can reconcile it into a single, ground-truth inventory that powers prioritization, design-time security, and audit-ready evidence.
How do you want to run your pen tests?
Pick the path that fits your team today — automate in the platform or hire our Red Team.
Accelerate In-House with the Platform
Automate the prep: Unified scanning, reachability-driven triage, CI/CD policy gates, and one-click evidence so testers start where the signal is.
- Source+binary analysis
- Reachability + intel = the 1%
- CI/CD + audit-ready evidence
Hire Our Red Team
Full‑service engagements using the same platform, delivered by expert attackers.
- End-to-end management
- Exploit development expertise
- Executive + technical reporting
Complete Medical Device Security Solution
A single, continuous workflow from premarket submission to post-market surveillance built for patient safety and regulatory trust.
Get real-time exploit intelligence with EPSS scores, threat actor tracking, and weaponized exploit detection. Understand which vulnerabilities are actively being exploited in the wild.
- EPSS probability scores
- Weaponized exploit detection
- Threat actor attribution
- KEV catalog integration
Security Where Developers Already Work
Integrate security into existing developer workflows—without slowing delivery.
CI/CD Integration: Embed security scanning directly into existing CI/CD pipelines with native support for Jenkins, GitHub Actions, GitLab CI, and other common tooling.
Developer Tools: Use command-line tools, IDE plugins, and APIs that fit naturally into developer workflows without slowing delivery.
API-First Architecture: Build custom integrations and automation workflows using REST and GraphQL APIs tailored to your environment.
Policy as Code: Define security policies as code, version them alongside applications, and enforce them automatically at build time.
Request a Unified SBOM Audit
Get a living SBOM view of your product portfolio—prioritized, compliant, and audit-ready.
What Our Customers Say
See how Finite State helps organizations strengthen product security and meet compliance requirements.
See the Real Exposure on Your Product
Bring a build (and supplier SBOMs, if available). We’ll show how it becomes audit-ready proof.