The Open Source Trojan Horse — Hidden Risk in Reused Code
Open source powers IoT, but hidden components and transitive risks expose your products. Learn how to secure what you didn’t even know you shipped.
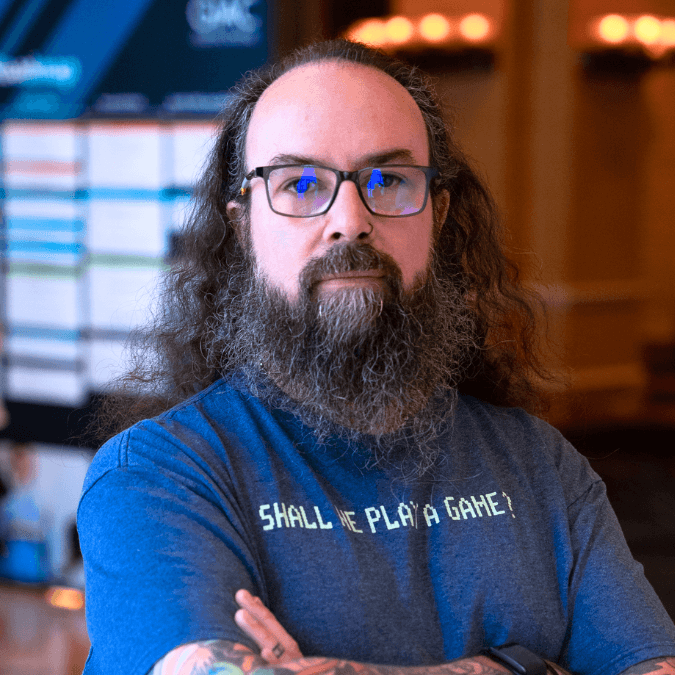
Larry Pesce
VP of Services
The Double-Edged Sword of OSS in IoT
Embedded systems run on open source. From kernels to TLS stacks to web interfaces, we build faster and smarter because someone else already wrote the code.
But here’s the catch: that someone else didn’t write it for your threat model. Or your regulatory environment. Or your customer’s peace of mind. And often, you’re not even sure what they wrote. Because the deeper the dependency tree goes, the murkier it gets.
The Hidden Cost of Convenience
Using OSS isn’t the problem. Not knowing what it’s doing is. Here’s how reused code can betray you:
- Transitive Dependencies: You pull in Lib A, which pulls in Lib B, which pulls in... Log4j. Oops.
- Undeclared Components: Binaries can include content that never shows up in manifests.
- Version Drift: You think you’re using the safe version. The binary you shipped says otherwise.
And the worst part? Traditional scanners only catch what’s declared or obvious. If it’s buried deep in a third-party blob, you’re in the dark.
The Log4j Hangover
Years after the Log4j meltdown, orgs are still finding it in their products. Why? Because it was tucked away inside some helper utility... inside a third-party library... inside a binary they didn’t write and never scanned.
That’s the reality of open source in embedded: deep dependencies, minimal visibility, massive exposure.
OSS Isn’t the Enemy — But Blind Use Is
We love open source. This isn’t about fear. It’s about visibility. You can’t protect what you don’t know is there.
What you need:
- Full-binary inspection: So you can see what’s statically linked in—even if it wasn’t declared.
- Cross-component reachability analysis: Are those vulnerabilities actually exploitable?
- Continuous SBOM regeneration: Every build. Every time. With binary validation.
How to Take Control
- Inventory everything. Don’t just trust manifests—verify through binary inspection.
- Scan the code and the compiled output. Both tell different parts of the story.
- Treat OSS like third-party risk. Because it is.
Final Word
Open source accelerates innovation. It also amplifies risk if you don’t inspect what you inherit, and in the next era of IoT security, transparency is power.
Up next: Wrapping it all up with a roadmap for the modern IoT security stack.
{{cta('190840854344')}}
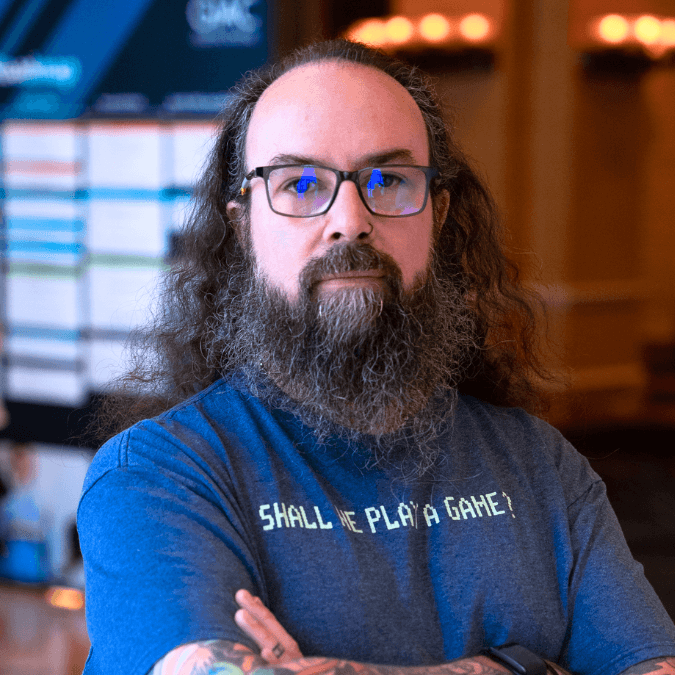
Larry Pesce
VP of Services
Larry Pesce is a lifelong hacker, educator, and leader in embedded and connected device security. As the Vice President of Services, Larry drives strategic security initiatives across the software supply chain, helping product teams build resilient devices from the ground up. With over 15 years of hands-on penetration testing experience spanning IoT, healthcare, ICS/OT, and wireless technologies, he combines deep technical knowledge with real-world expertise. Larry is also a renowned SANS instructor and co-host of the long-running Paul’s Security Weekly podcast, shaping the next generation of security professionals.